How ERP Systems Safeguard Business-Critical Data

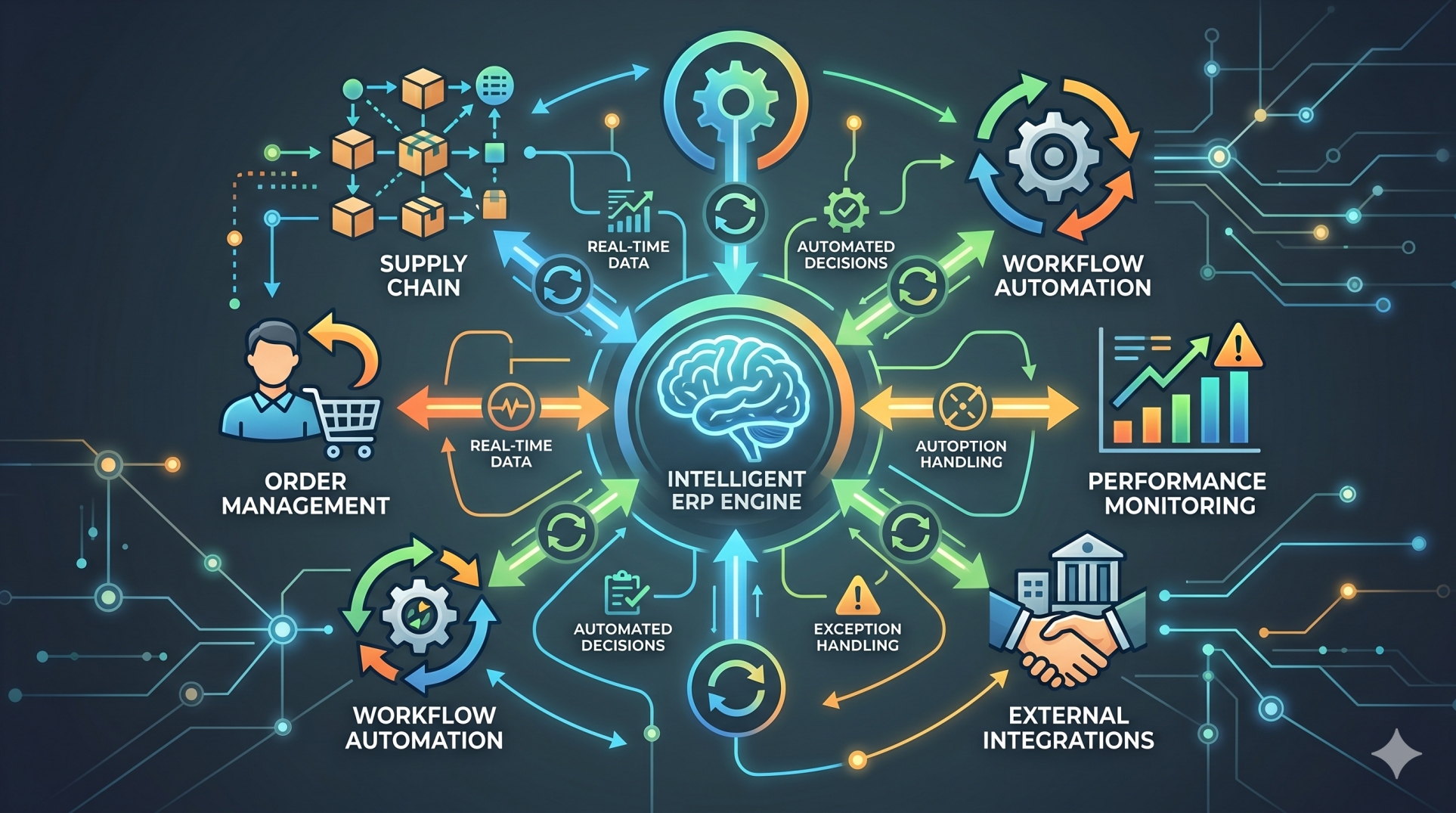
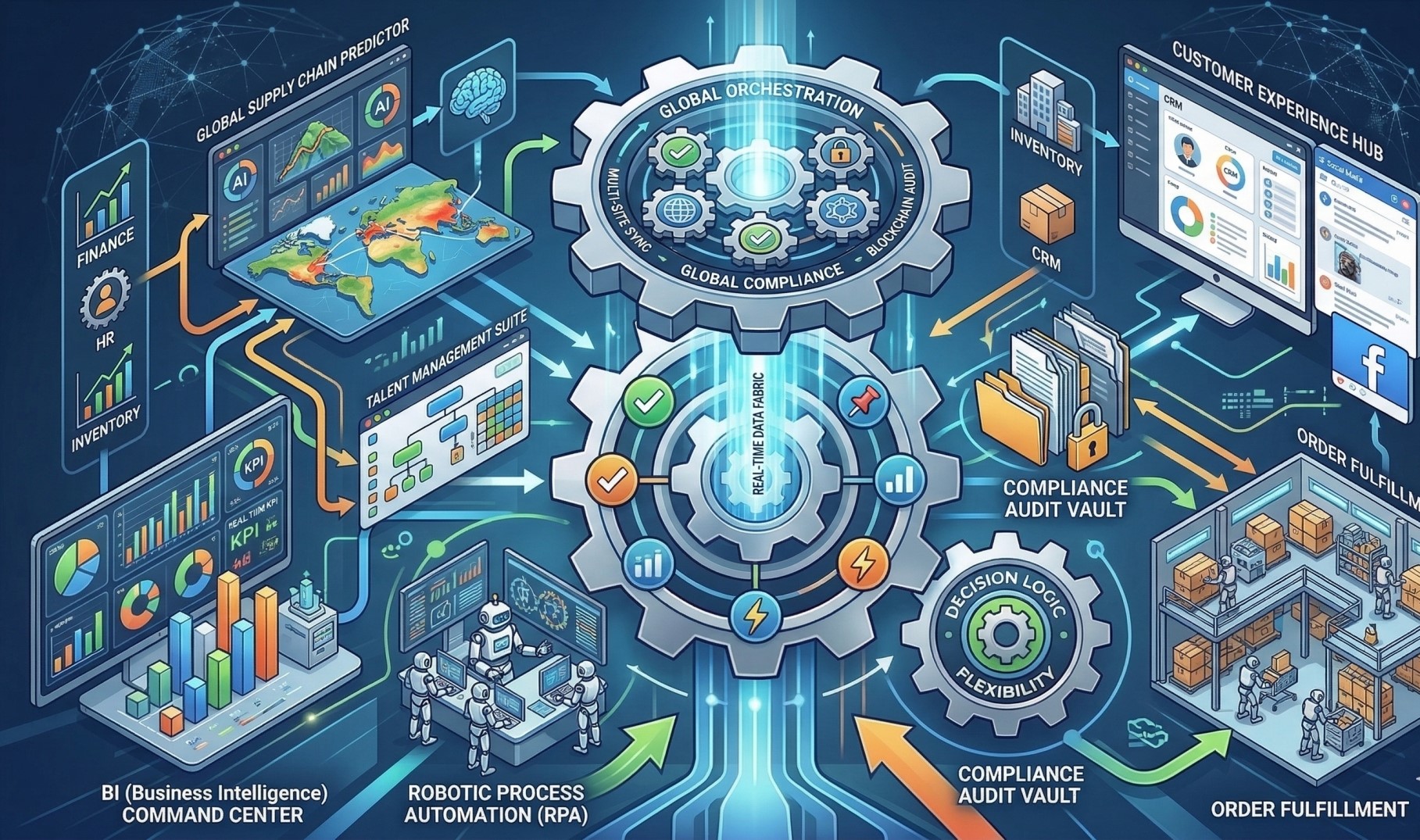
Enterprise Resource Planning platforms store and process some of the most valuable information within an organization, including financial statements, employee records, customer databases, vendor agreements, and operational metrics. As digital operations expand, ERP systems function as the central security layer that protects this data from misuse, cyber threats, operational errors, and compliance risks. Modern ERP environments combine technical safeguards, governance controls, and monitoring systems to maintain data integrity and resilience.
Step 1: Unified Data Governance 🗂️🔐
• Brings core business data into a controlled, centralized environment 🏢
• Reduces risks associated with disconnected legacy systems 🔄
• Applies consistent security standards across departments 📏
• Limits uncontrolled duplication of sensitive records 📄
• Improves visibility and administrative oversight 👀
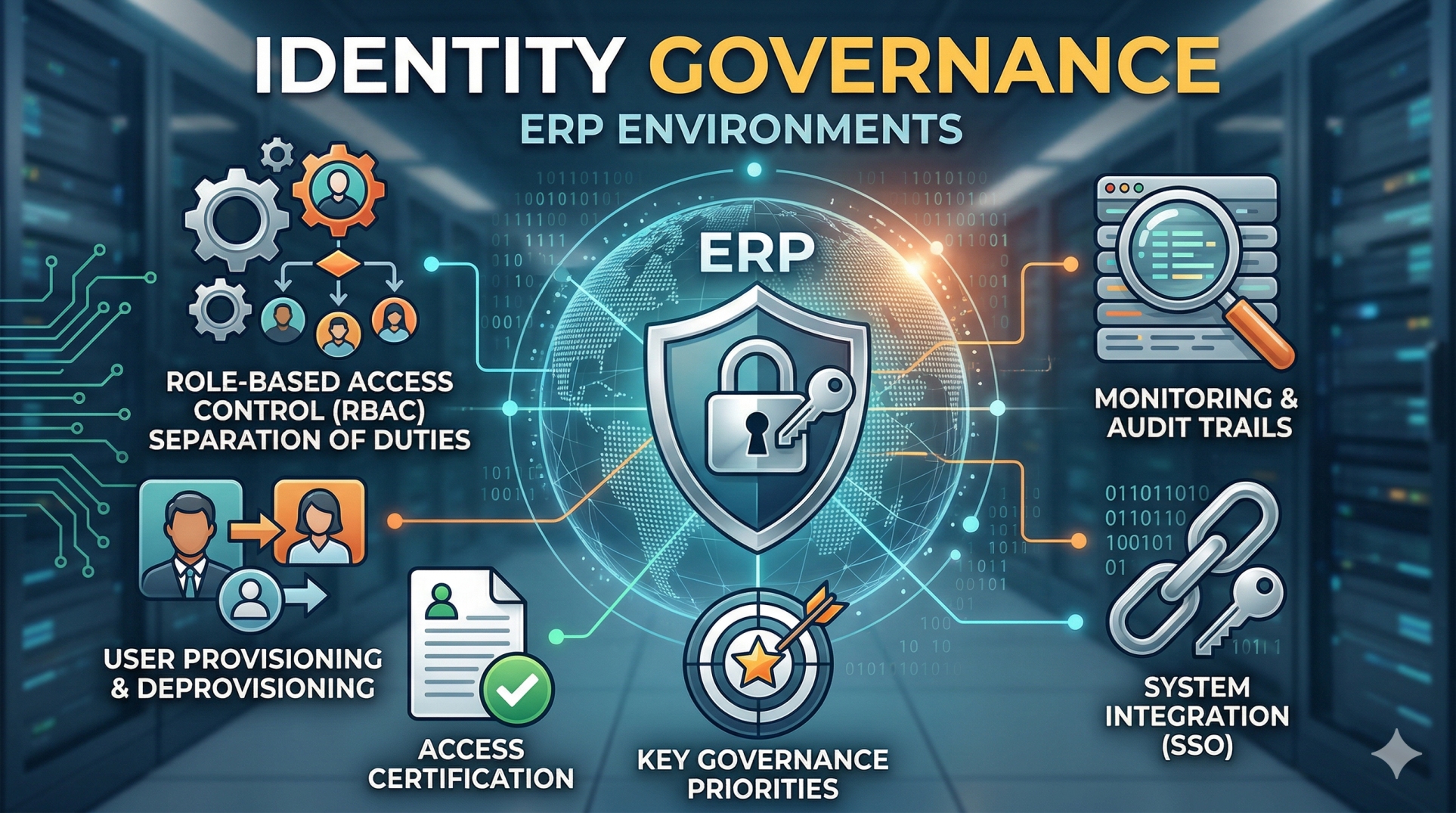
Step 2: Controlled Access Through Role Definition 👤🔒
• Grants system access based on defined job roles 🧾
• Enforces least-privilege access across departments ⚖️
• Prevents unauthorized editing or exposure of sensitive records 🚫
• Separates critical responsibilities to reduce fraud risk 🔍
• Minimizes insider-related vulnerabilities 🛡️
Step 3: Strong Identity and Authentication Measures 🔑🛡️
• Implements secure credential policies and login controls 🔐
• Supports multi-factor authentication for elevated permissions 📲
• Connects with enterprise identity and access management systems 🔗
• Monitors login attempts and unusual access behavior 👁️
• Reduces the likelihood of unauthorized system entry 🚪
Step 4: Encryption and Secure Data Handling 🔐📡
• Protects stored data using encryption protocols 🧩
• Secures information transmitted across internal and external networks 🌐
• Shields confidential financial and personal data from interception 🛑
• Adheres to modern cryptographic security standards 📜
• Strengthens defense against external cyber threats ⚔️
Step 5: Continuous Monitoring and Audit Logging 📊🕵️
• Maintains detailed logs of user actions and system events 🗒️
• Enables traceability for financial and operational transactions 🔍
• Supports compliance audits and internal investigations 📑
• Detects irregular patterns or suspicious activity 🚨
• Reinforces accountability throughout the organization 🏛️
Step 6: Data Backup and Operational Resilience 💾⚙️
• Performs automated and scheduled data backups 🔄
• Enables rapid restoration in case of system failure ⚡
• Protects against ransomware and data corruption 🛡️
• Supports disaster recovery frameworks 🌍
• Maintains continuity during unexpected disruptions ⏱️
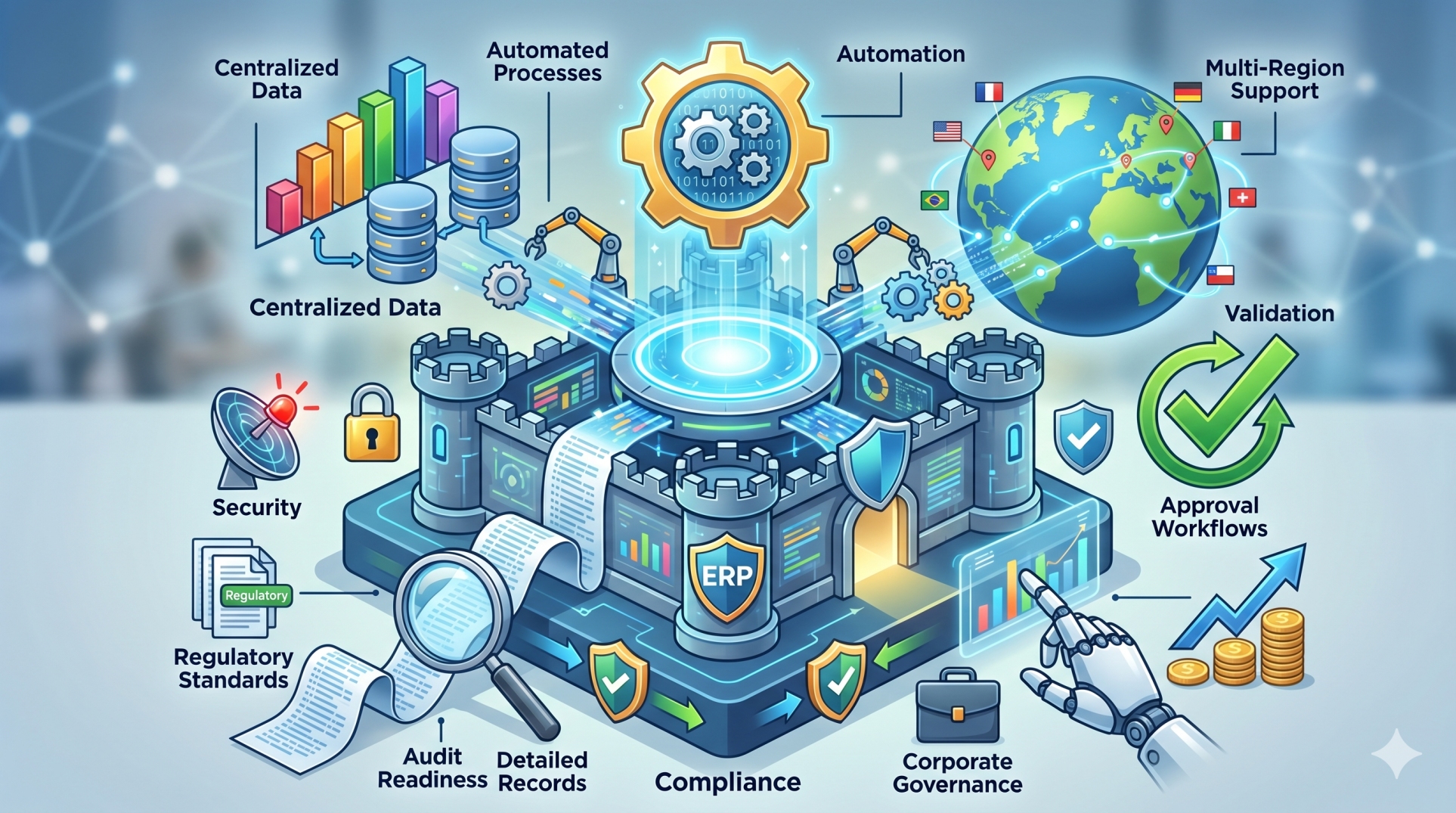
Step 7: Regulatory Compliance and Policy Enforcement 📜⚖️
• Supports alignment with financial and privacy regulations 🏢
• Enforces structured data retention policies 🗃️
• Protects confidential and personally identifiable information 🔒
• Generates documentation for regulatory reporting 📄
• Reduces exposure to legal penalties and compliance risks ⚠️
Step 8: Core Business Protection Outcomes 🏆🛡️
• Shields financial, payroll, and customer data from breaches 🔐
• Reduces fraud risk through controlled monitoring 👁️
• Preserves stakeholder trust and brand reputation 🤝
• Protects strategic and operational assets 📊
Conclusion
ERP systems function as the protective foundation of modern enterprises by securing the information that drives decision-making, operations, and growth. Through structured access control, encryption, monitoring, and compliance support, ERP platforms help organizations manage risk while maintaining reliability and trust. As digital transformation accelerates and cyber threats become more sophisticated, strong ERP security is not optional—it is essential to sustainable business operations.
See more blogs
You can all the articles below






























































.png)


.png)

