Role of Access Control in ERP Systems

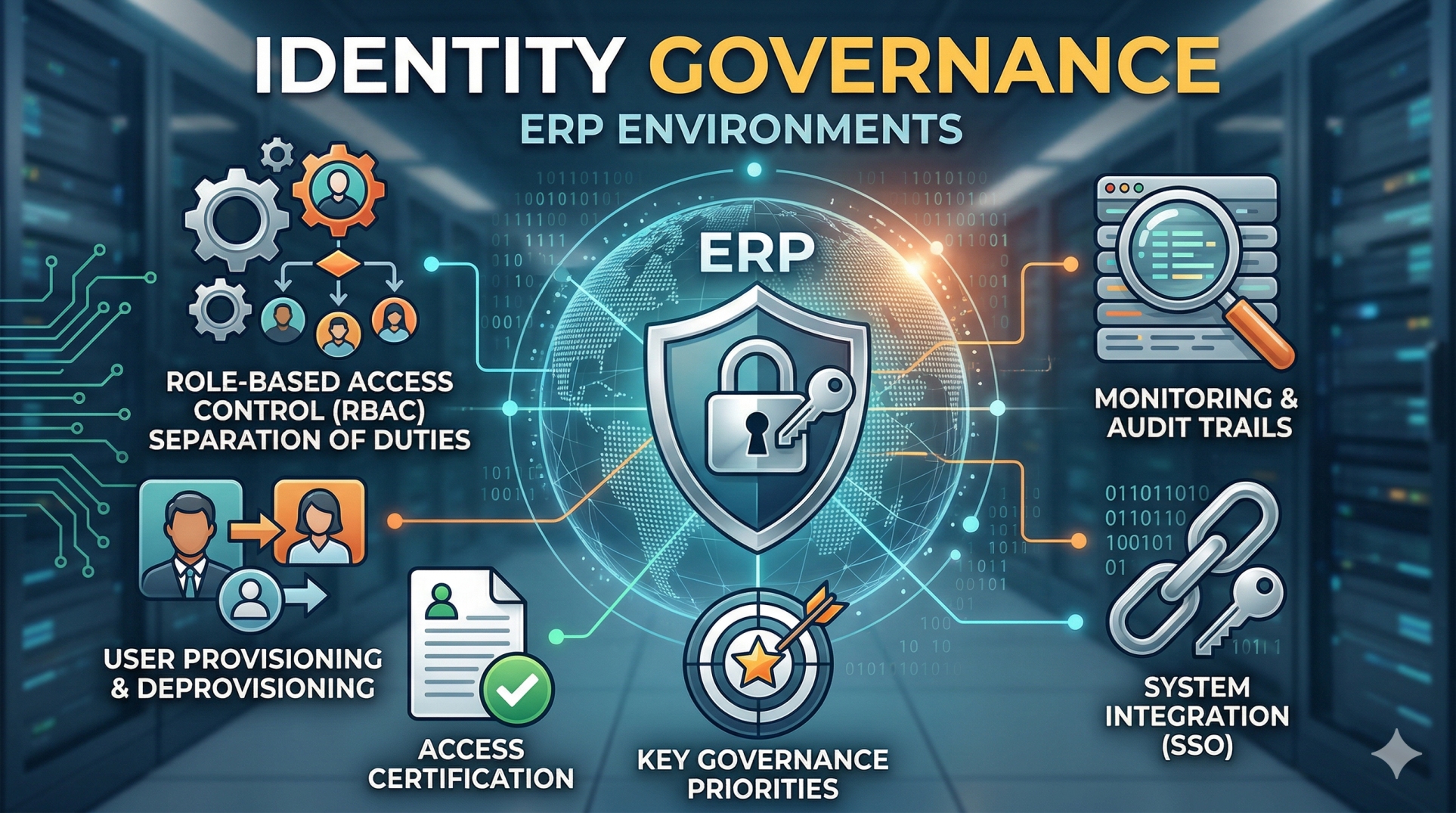
Enterprise Resource Planning systems centralize critical financial, operational, and strategic data. Because ERP platforms manage sensitive information across departments, access control is not just a technical feature—it is a foundational governance mechanism. Proper access control ensures that the right individuals have appropriate permissions while protecting the organization from risk, fraud, and compliance violations.
1. Protecting Sensitive Business Data 🔐
• Restricts access to confidential financial and operational records 🗂️
• Prevents unauthorized viewing or modification of critical information 🚫
• Safeguards intellectual property and strategic plans 📘
• Reduces exposure to internal and external threats ⚠️
• Strengthens overall data security posture 🛡️
2. Role-Based Access Control (RBAC) 🏷️
• Assigns permissions based on job roles rather than individuals 👥
• Simplifies management of user privileges ⚙️
• Ensures consistent permission structures across departments 🏢
• Minimizes errors in manual permission assignments ✍️
• Supports scalable user management as the organization grows 📈
3. Segregation of Duties (SoD) ⚖️
• Prevents conflicts of interest in financial and operational processes 🔄
• Ensures no single user controls an entire transaction lifecycle 🔍
• Reduces fraud and internal misuse risks 🚨
• Supports compliance with regulatory standards 📜
• Strengthens internal audit frameworks 📊
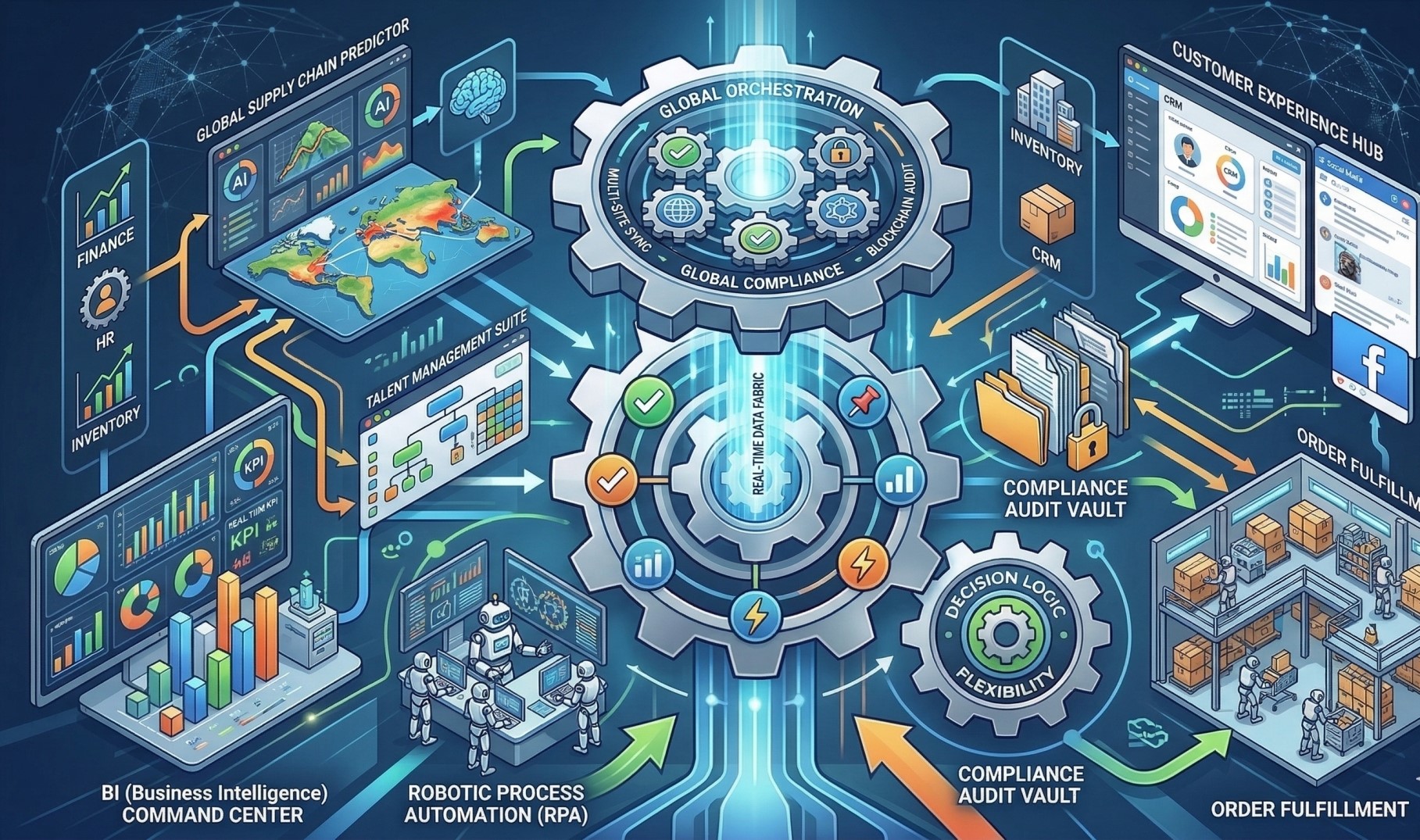
4. Minimizing Operational Risk 🚧
• Limits system access to necessary functions only 🔒
• Reduces accidental data deletion or modification 🧾
• Controls high-risk activities such as approvals and payments 💳
• Enhances system stability and reliability ⚙️
• Prevents misuse of administrative privileges 👤
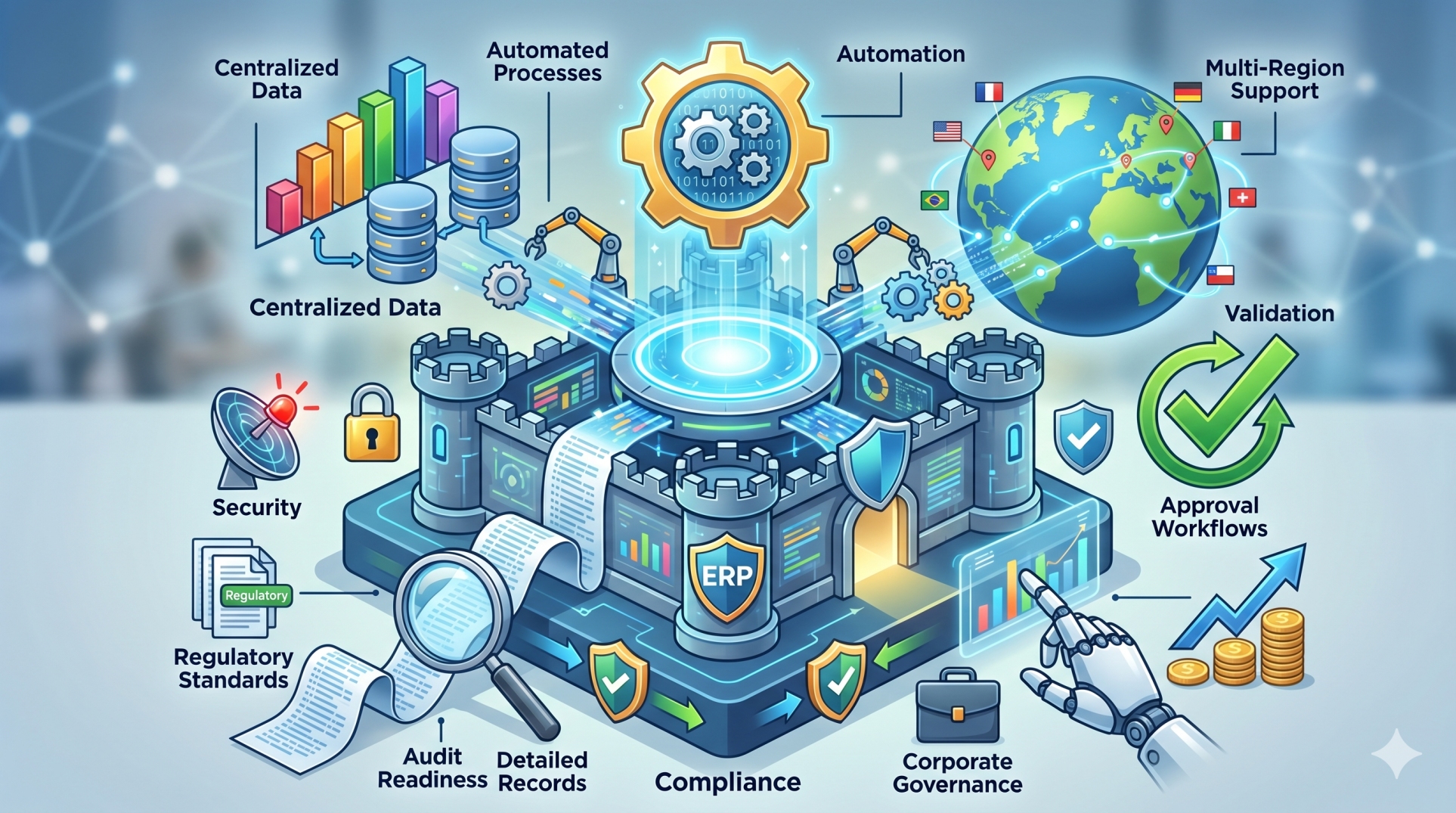
5. Compliance and Regulatory Alignment 📋
• Supports adherence to financial and data protection regulations 📑
• Maintains detailed access logs for audit purposes 🗃️
• Demonstrates accountability in user activity tracking 🧠
• Aligns with internal governance policies 🏛️
• Facilitates smoother external audits 🔍
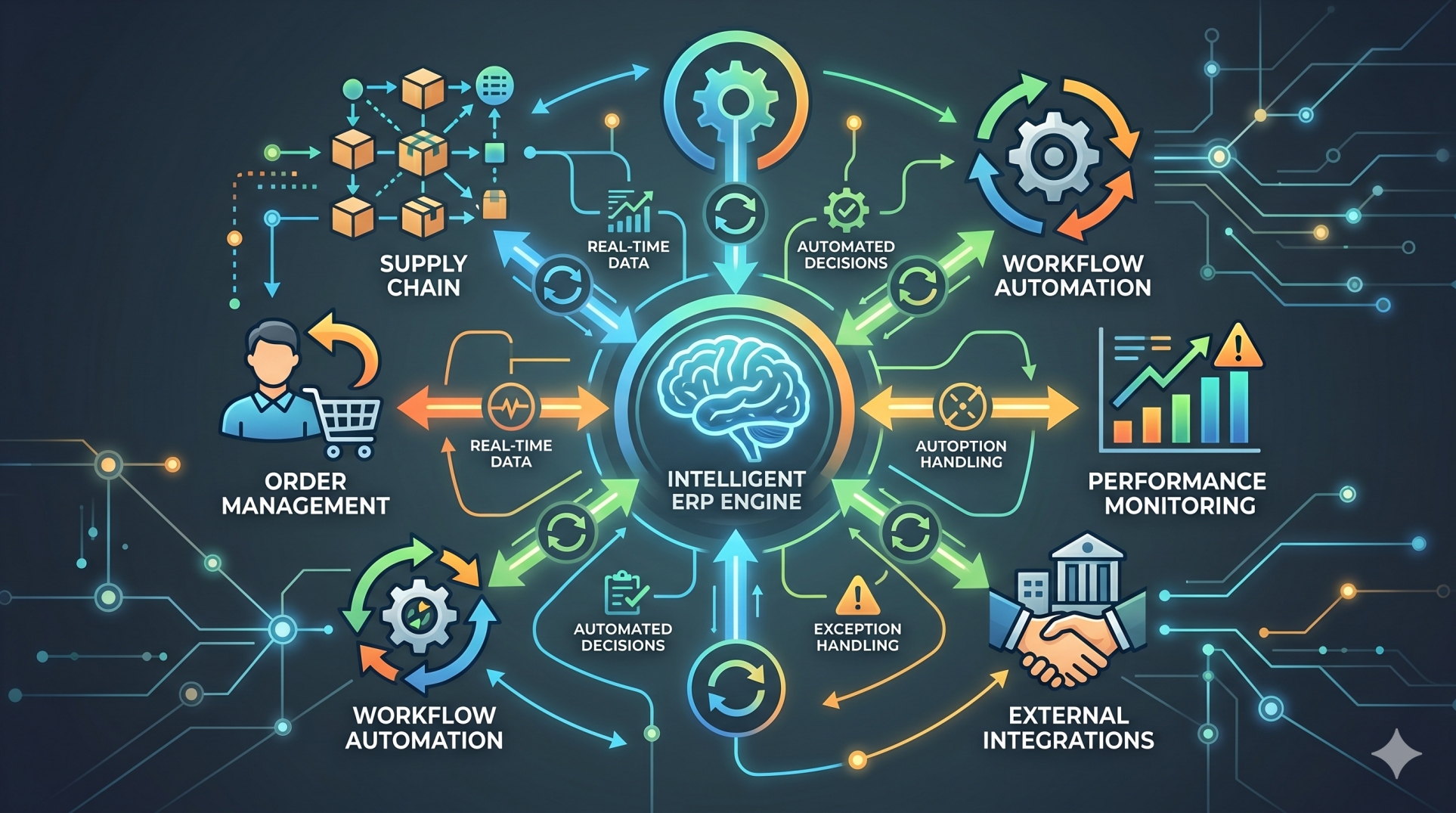
6. Monitoring and Activity Tracking 👀
• Records user actions across modules and transactions 📝
• Detects unusual or suspicious access patterns 🚨
• Enables real-time alerts for high-risk behavior ⏱️
• Supports forensic investigations when needed 🔎
• Improves transparency across system usage 📊
7. Managing Access in Multi-Department Environments 🌍
• Controls cross-departmental visibility of sensitive data 🔐
• Supports hierarchical access structures 🏢
• Ensures regional or subsidiary-level restrictions 🌐
• Maintains data boundaries within global organizations 🗂️
• Enables scalable permission management 📈
8. Strategic Importance of Access Control 🎯
• Protects financial integrity and operational continuity 💰
• Prevents costly compliance violations and penalties ⚖️
• Reduces fraud exposure and internal risk 🚫
• Builds trust in ERP-driven decision-making 🤝
9. Access Control in Cloud ERP Environments ☁️
• Enforces secure authentication mechanisms 🔑
• Supports multi-factor authentication for critical roles 📲
• Integrates with identity management systems 🔗
• Protects remote and distributed user access 🌐
• Enhances resilience against cyber threats 🛡️
10. Access Control as a Governance Framework 🏛️
• Moves beyond IT configuration into enterprise governance 📊
• Aligns system permissions with business accountability 🧩
• Supports long-term risk management strategy 📈
• Strengthens executive oversight of enterprise systems 👔
• Positions ERP as a secure operational backbone 🏗️
Conclusion
Access control is central to the effectiveness and integrity of ERP systems. By implementing structured permission models, segregation of duties, and continuous monitoring, organizations protect sensitive data while maintaining operational efficiency. Strong access governance ensures that ERP platforms remain secure, compliant, and reliable as the organization grows and evolves.
See more blogs
You can all the articles below






























































.png)


.png)

