Insider Risk Mitigation Through ERP Controls

As organizations become increasingly data-driven, insider risks—whether intentional or accidental—pose a significant threat to operational integrity, financial security, and regulatory compliance. Enterprise Resource Planning (ERP) systems sit at the core of business operations, making them a critical control point for mitigating these risks. By implementing robust ERP controls, organizations can proactively detect, prevent, and respond to insider threats while maintaining trust and accountability.
Step 1: Understanding Insider Risk in ERP Environments 🔍
• Insider risks include unauthorized access, data misuse, and privilege abuse ⚠️
• Threats can originate from employees, contractors, or partners 👥
• Risks may be intentional (fraud, sabotage) or unintentional (errors, negligence) ⚖️
• ERP systems centralize sensitive financial and operational data 🗂️
• Visibility into user actions is essential for early risk detection 👁️
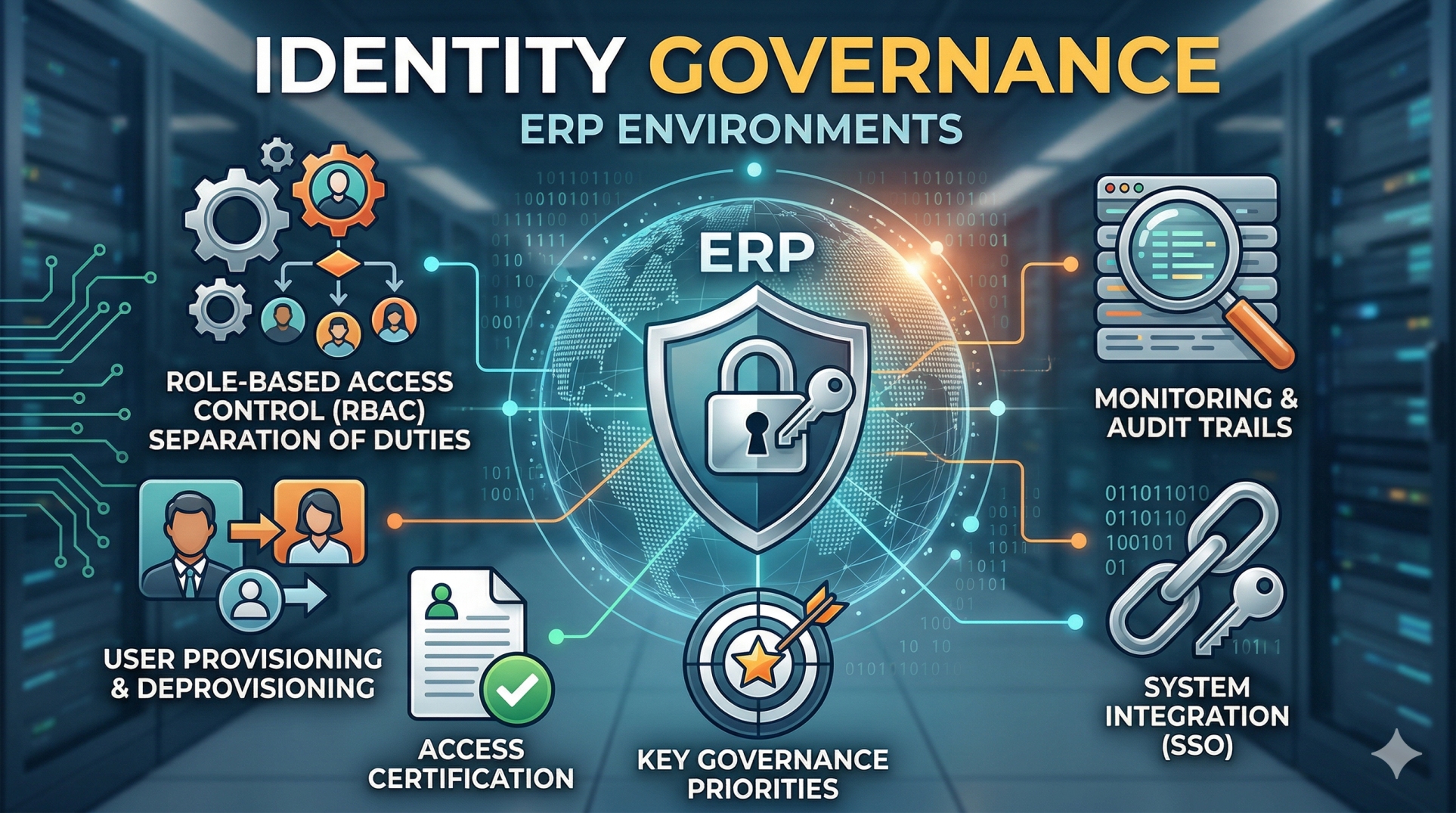
Step 2: Implementing Role-Based Access Control (RBAC) 🔐
• Assign system access based on job roles and responsibilities 🧑💼
• Restrict access to sensitive data and critical functions 🚫
• Enforce the principle of least privilege across all users ⚖️
• Regularly review and update access rights 🔄
• Prevent unauthorized escalation of privileges ⛔
Step 3: Segregation of Duties (SoD) Enforcement ⚙️
• Separate critical tasks to reduce risk of fraud or misuse 🔀
• Ensure no single user controls end-to-end financial processes 💰
• Define clear boundaries between roles and responsibilities 📊
• Use ERP controls to detect SoD conflicts automatically 🤖
• Continuously monitor and resolve violations 🚨
Step 4: Real-Time Monitoring and Audit Trails 📡
• Track user activities across all ERP modules in real time ⏱️
• Maintain detailed audit logs for every transaction 🧾
• Enable alerts for suspicious or unusual behavior 🚨
• Support forensic analysis and compliance audits 🔍
• Ensure transparency in all system interactions 👁️
Step 5: Data Access and Usage Controls 📂
• Limit access to sensitive financial and customer data 🔒
• Implement data masking and encryption where necessary 🔐
• Control data exports, downloads, and sharing 📤
• Monitor how data is accessed and used across the system 📊
• Prevent unauthorized data leakage or exfiltration 🚫
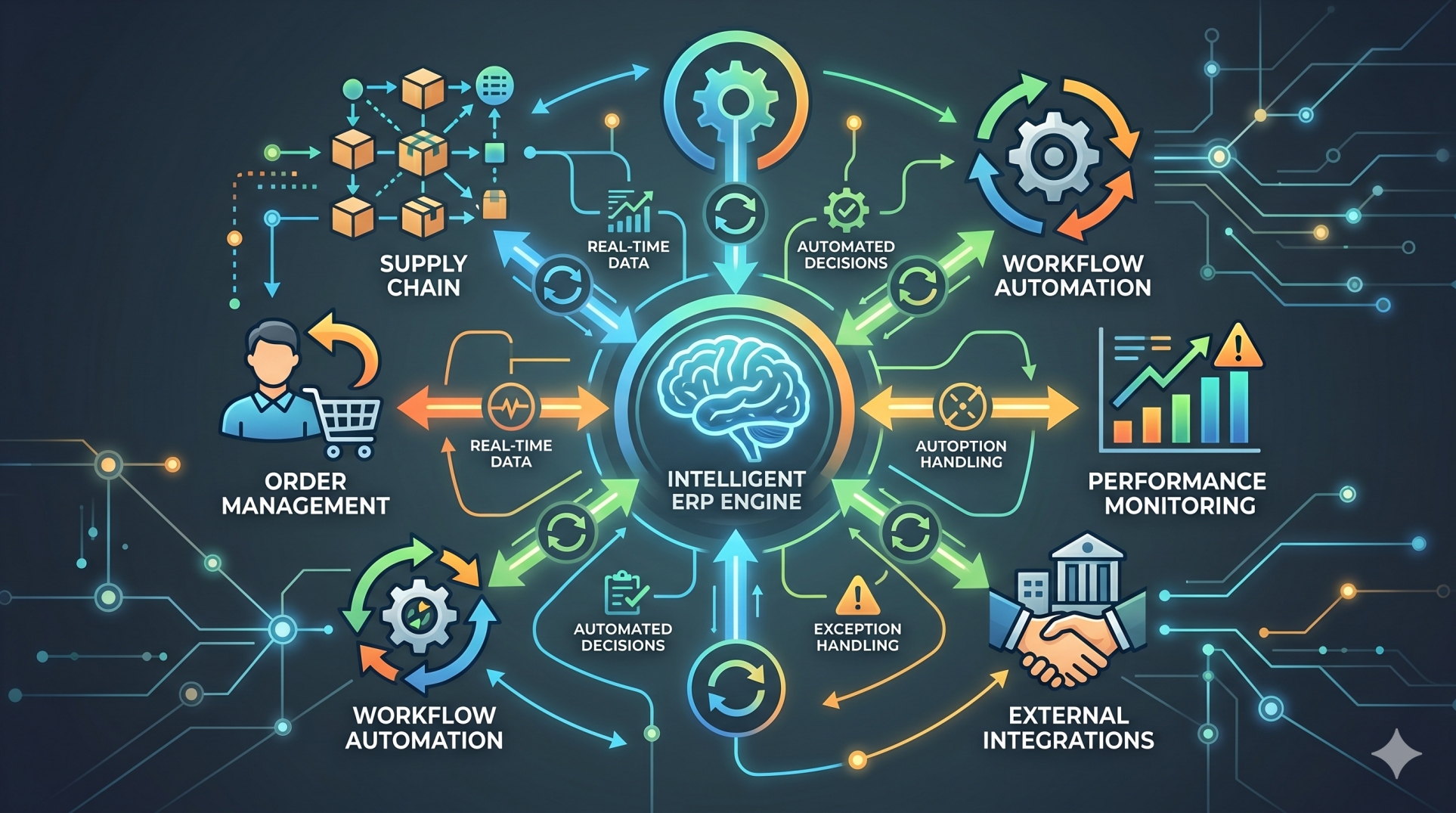
Step 6: Workflow Approvals and Authorization Controls ✅
• Enforce multi-level approval workflows for critical actions 🧾
• Validate transactions before execution ✔️
• Automate approval chains based on business rules ⚙️
• Reduce the risk of unauthorized or fraudulent activities 🚫
• Maintain accountability for all approvals 👥
Step 7: Anomaly Detection and Behavioral Analytics 🤖
• Use analytics to identify unusual user behavior patterns 📊
• Detect deviations from normal activity baselines ⚠️
• Leverage AI-driven insights for proactive risk detection 🤖
• Identify potential insider threats before escalation 🚨
• Continuously refine detection models based on data 📈
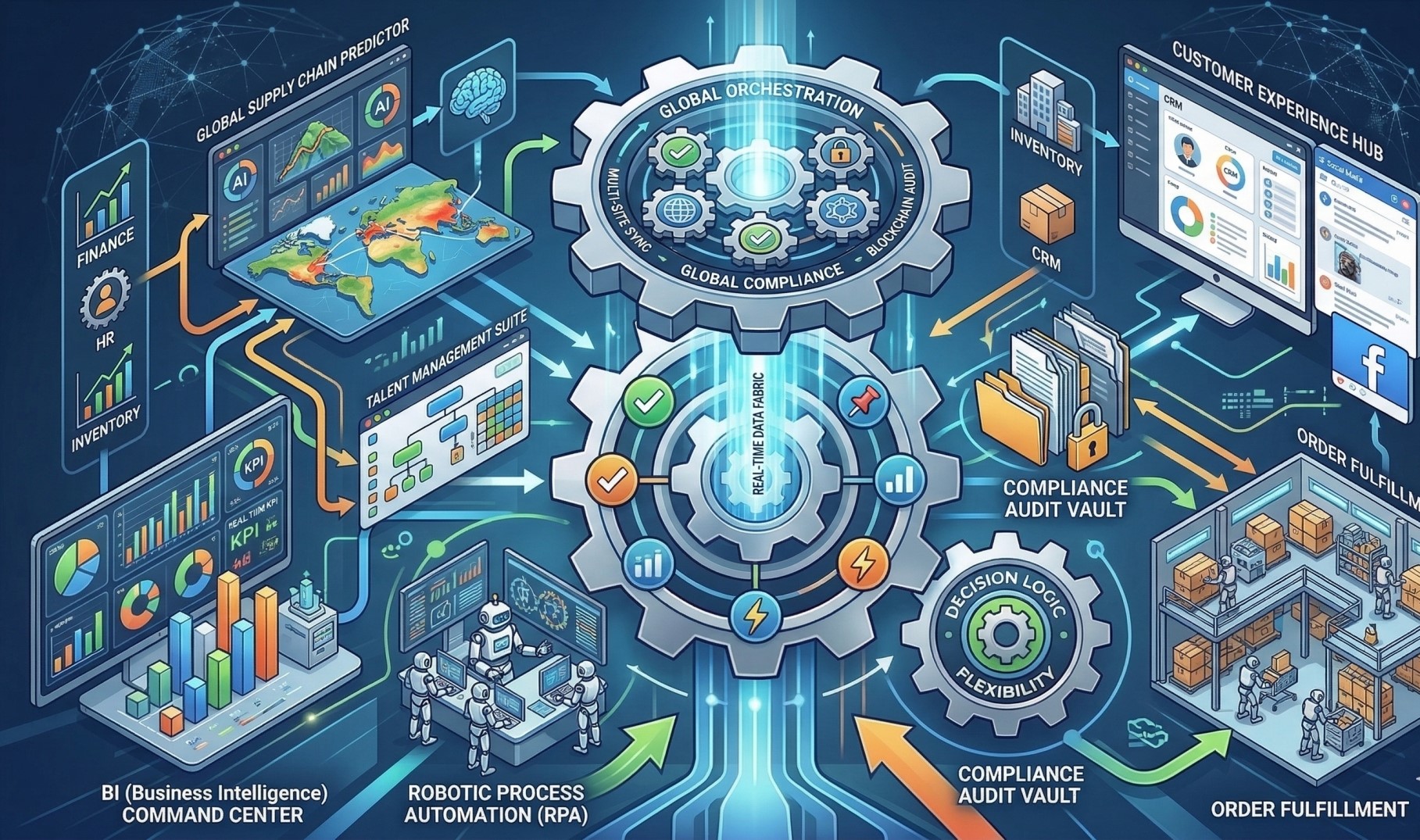
Step 8: Key Risk Mitigation Priorities 📊
• Strong access control and identity management 🔐
• Continuous monitoring and real-time visibility 👁️
• Automated enforcement of compliance policies 📜
• Scalable security frameworks aligned with business growth 🚀
Step 9: Incident Response and Risk Handling 🚨
• Establish clear protocols for handling insider incidents 📋
• Enable rapid investigation using audit logs 🔍
• Isolate affected systems or users when necessary 🚫
• Document incidents for compliance and improvement 🧾
• Continuously enhance response strategies based on lessons learned 🔄
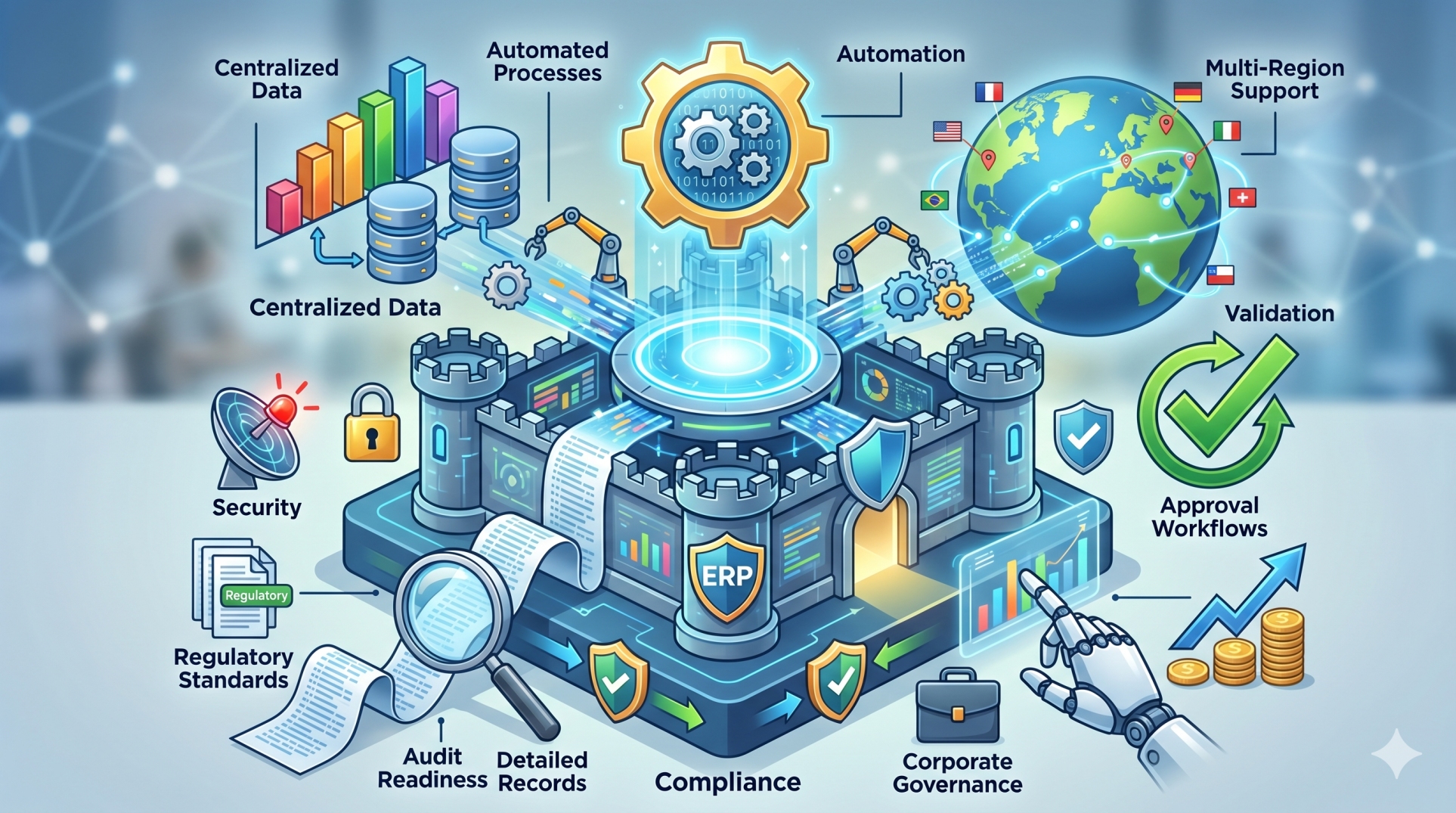
Step 10: Building a Secure ERP Governance Framework 🏛️
• Define governance policies for ERP security and usage 📜
• Align controls with industry standards and regulations 🏛️
• Conduct regular risk assessments and audits 🔍
• Train employees on security best practices 🎓
• Foster a culture of accountability and awareness 🤝
Conclusion
Mitigating insider risk through ERP controls is essential for safeguarding business operations and sensitive data. By combining access management, monitoring, analytics, and governance, organizations can create a secure ERP environment that minimizes risk while enabling productivity. A proactive and structured approach not only protects against internal threats but also strengthens overall organizational resilience in an increasingly complex digital landscape.
See more blogs
You can all the articles below

























































.png)


.png)

